What Is EDR in Cyber Security: Overview & Capabilities
eSecurity Planet
SEPTEMBER 24, 2024
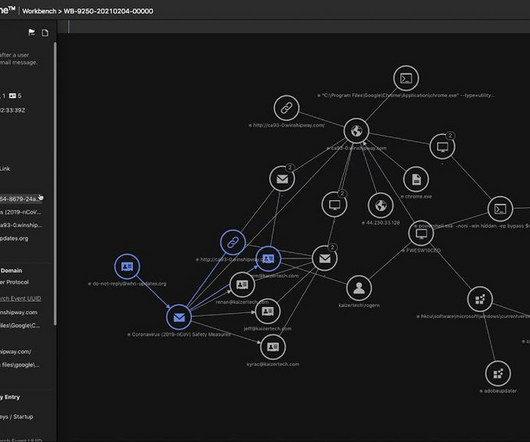
Configuring the EDR tool: Tailor the EDR policies according to your organization’s specific security requirements. This step provides configurable flexibility for best performance. Organizations can use this information to avoid emerging threats and improve their overall security posture. This is where EDR steps in.











Let's personalize your content