Vietnam-linked Bismuth APT leverages coin miners to stay under the radar
Security Affairs
DECEMBER 1, 2020
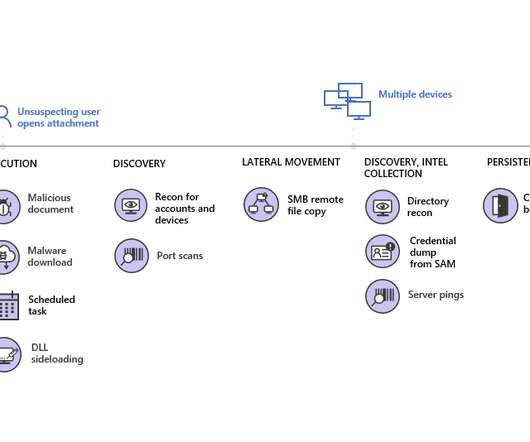
Learn how the group tried to stay under the radar using threats perceived to be less alarming: [link] — Microsoft Security Intelligence (@MsftSecIntel) November 30, 2020. “To perform DLL sideloading, BISMUTH introduced outdated versions of various applications, including Microsoft Defender Antivirus.












Let's personalize your content