EDR vs EPP vs Antivirus: Comparing Endpoint Protection Solutions
eSecurity Planet
JULY 31, 2024
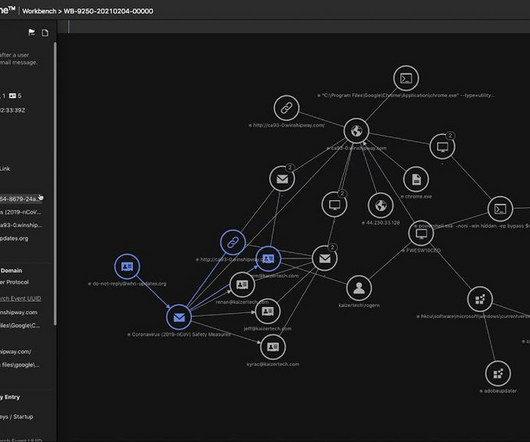
Endpoint protection solutions safeguard network endpoints against cyberthreats using a selection of management tools, including endpoint detection and response (EDR), endpoint protection platform (EPP), and antivirus (AV). AV software blocks malware, EPP passively prevents threats, and EDR actively mitigates network attacks.




















Let's personalize your content