500M Avira Antivirus Users Introduced to Cryptomining
Krebs on Security
JANUARY 8, 2022
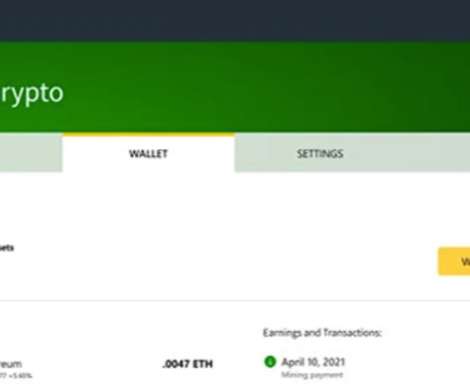
Many readers were surprised to learn recently that the popular Norton 360 antivirus suite now ships with a program which lets customers make money mining virtual currency. Avira Free Antivirus). “Avira Crypto allows you to use your computer’s idle time to mine the cryptocurrency Ethereum (ETH),” the FAQ explains.













Let's personalize your content