‘Fix It’ social-engineering scheme impersonates several brands
Malwarebytes
DECEMBER 19, 2024
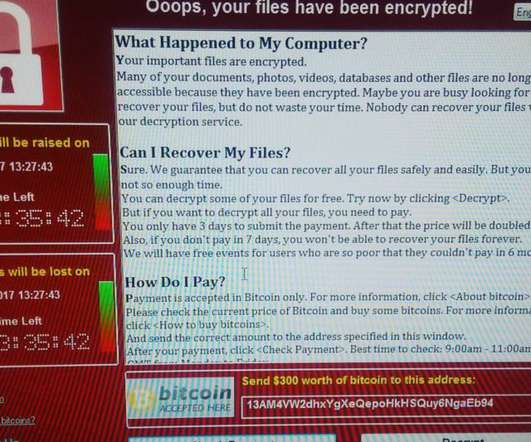
More and more, threat actors are leveraging the browser to deliver malware in ways that can evade detection from antivirus programs. Social engineering is a core part of these schemes and the tricks we see are sometimes very clever. Oddly, we saw a lure for a cruise booking site.
















Let's personalize your content