Google reveals new cloud security features at RSA 2020
Tech Republic Security
FEBRUARY 24, 2020
Google's reCAPTCHA Enterprise and Web Risk API get a general release; Chronicle Security gets boosts from new threat detection and timelining features.
This site uses cookies to improve your experience. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country, we will assume you are from the United States. Select your Cookie Settings or view our Privacy Policy and Terms of Use.
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.
Used for the proper function of the website
Used for monitoring website traffic and interactions
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.

Tech Republic Security
FEBRUARY 24, 2020
Google's reCAPTCHA Enterprise and Web Risk API get a general release; Chronicle Security gets boosts from new threat detection and timelining features.

We Live Security
FEBRUARY 8, 2021
A view of the Q4 2020 threat landscape as seen by ESET telemetry and from the perspective of ESET threat detection and research experts. The post ESET Threat Report Q4 2020 appeared first on WeLiveSecurity.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Anton on Security
OCTOBER 7, 2020
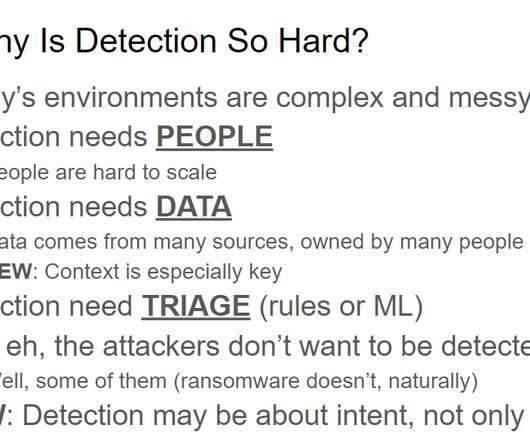
While creating a recent presentation, I needed a slide on “threat detection is hard.” And it got me thinking, why is threat detection so hard for so many organizations today? This means we are “celebrating” ~35 years of cyber threat detection. This does make detection even harder. Action items?

Security Boulevard
FEBRUARY 1, 2022
2020 was a tipping point; the first year where we saw more cloud asset breaches and incidents than on-premises ones. We know bad actors are out there; if you’re operating in the cloud, how are you detecting threats? The post Real-Time Threat Detection in the Cloud appeared first on Security Boulevard.

SecureList
MARCH 31, 2021
2020 was challenging for everyone: companies, regulators, individuals. As a result, 2020 was extremely eventful in terms of digital threats, in particular those faced by financial institutions. In 2020, the group tried its hand at the big extortion game with the VHD ransomware family. Key findings. to 13.21%.
Security Affairs
MARCH 22, 2021
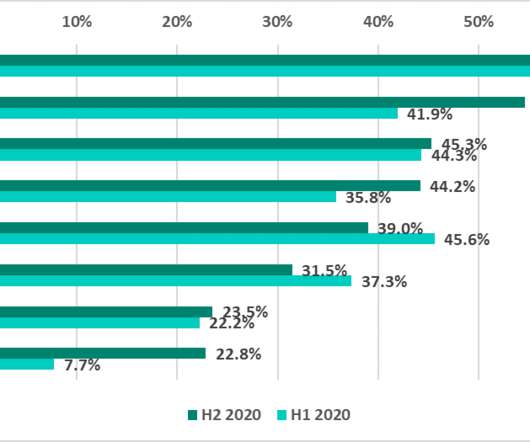
The Kaspersky ICS CERT published a report that provided details about the threat landscape for computers in the ICS engineering and integration sector in 2020. Kaspersky ICS CERT published a report that provided details about the threat landscape for ICS engineering and integration sector in 2020. In H2 2020, 39.3%

CyberSecurity Insiders
MARCH 10, 2021
BitDam offers Advanced Threat Protection (ATP) solution that enables customers to protect their IT infrastructure against malware, phishing and ransomware. In November 2020, SolarWinds, an IT software company was hit by a data breach where hackers infiltrated its database through vulnerability in Orion Software.

Anton on Security
DECEMBER 20, 2021
Skills, Not Tiers” “Beware: Clown-grade SOCs Still Abound”” “Revisiting the Visibility Triad for 2020” Top 5 posts with the most Medium fans : “Security Correlation Then and Now: A Sad Truth About SIEM” “Beware: Clown-grade SOCs Still Abound” “Can We Have “Detection as Code”?” “Why Why Is Threat Detection Hard?” “A

Anton on Security
NOVEMBER 20, 2020
Top 3 most popular posts of all times: “Security Correlation Then and Now: A Sad Truth About SIEM” “Beware: Clown-grade SOCs Still Abound” “Can We Have “Detection as Code”?” Security operations / detection & response: “Can We Have “Detection as Code”?” “Top Why is Threat Detection Hard?”
Security Affairs
SEPTEMBER 18, 2020
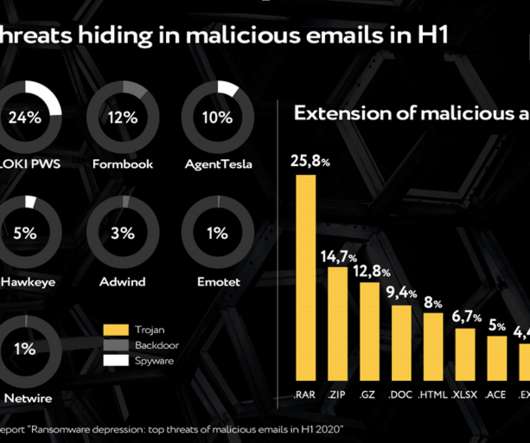
Singapore, 09/18/2020 — Group-IB , a global threat hunting and intelligence company headquartered in Singapore, evidenced the transformation of the threat portfolio over the first half of 2020. The post Ransomware en masse on the wane: top threats inside web-phishing in H1 2020 appeared first on Security Affairs.

Anton on Security
NOVEMBER 7, 2022
Why Is Threat Detection Hard?” Skills, Not Tiers”” “ New Paper: “Future of the SOC: Forces shaping modern security operations” ” “ Beware: Clown-grade SOCs Still Abound ” “Revisiting the Visibility Triad for 2020” “Stop Trying to Take Humans Out of SOC … Except … Wait… Wait… Wait…” “Why is Threat Detection Hard?” “A

Anton on Security
SEPTEMBER 16, 2021
Skills, Not Tiers” “Beware: Clown-grade SOCs Still Abound”” “New Paper: “Future of the SOC: Forces shaping modern security operations”” Top 5 posts with the most Medium fans : “Security Correlation Then and Now: A Sad Truth About SIEM” “Beware: Clown-grade SOCs Still Abound” “Can We Have “Detection as Code”?” “Why

Anton on Security
AUGUST 19, 2022
Why Is Threat Detection Hard?” “A A SOC Tried To Detect Threats in the Cloud … You Won’t Believe What Happened Next” Top 5 Cloud Security Podcast by Google episodes: Episode 1“Confidentially Speaking” Episode 47 “Megatrends, Macro-changes, Microservices, Oh My! Random fun new posts: “Detection as Code?

CSO Magazine
APRIL 21, 2021
Red Canary recently unveiled its 2021 Threat Detection Report. Included in the report is a mapping of many of the top cyberattack techniques to the MITRE ATT&CK framework. The findings presented by Red Canary researchers underscore the need to fully understand your network. Take the time to monitor what is normal in your firm.

McAfee
DECEMBER 4, 2020
2020 has been a tumultuous and unpredictable year, where we restructured our lives and redefined how we work and interact with each other. Although 2020 has undoubtedly been a year of trials and tribulations, I wanted to share some of McAfee’s top highlights. Ahead of the 2020 U.S. To support today’s U.S. Learn more here.

Anton on Security
MARCH 3, 2022
Skills, Not Tiers” “Beware: Clown-grade SOCs Still Abound”” “New Paper: “Future of the SOC: Forces shaping modern security operations” Top 5 posts with the most Medium fans : “Security Correlation Then and Now: A Sad Truth About SIEM” “Beware: Clown-grade SOCs Still Abound” “Can We Have “Detection as Code”?” “Why Right of SIEM? Get It Right!”
Anton on Security
MAY 15, 2023
Why Is Threat Detection Hard?” New Paper: “Future of the SOC: SOC People — Skills, Not Tiers”” “Revisiting the Visibility Triad for 2020” “ New Paper: “Future of the SOC: Forces shaping modern security operations” ” “ Beware: Clown-grade SOCs Still Abound ” “Why is Threat Detection Hard?” “A

Anton on Security
SEPTEMBER 27, 2024
Can We Have “Detection as Code”? Revisiting the Visibility Triad for 2020 (update for 2024 is coming soon BTW!) Beware: Clown-grade SOCs Still Abound Detection Engineering is Painful — and It Shouldn’t Be (Part 1) [now a 10 post series, not yet finished…] Why is Threat Detection Hard? Use Cloud Securely?
Anton on Security
AUGUST 9, 2023
Top 6 most popular posts of all times (these ended up being the same as last quarter, and a few quarters before) : “Security Correlation Then and Now: A Sad Truth About SIEM” “Can We Have “Detection as Code”?” “New Why Is Threat Detection Hard?” What Does This Even Mean?!” “How Is Your Fate In the Cloud?”

Malwarebytes
JUNE 9, 2022
The “Covid bounce” The 2022 Threat Review detailed the remarkable rebound in detection numbers for malware, adware and Potentially Unwanted Programs (PUPs) in 2021. Detections of all three went down during 2020, as pandemic restrictions created a huge increase in the number of people working from home.

Security Affairs
MARCH 8, 2021
via the unauthorized remote command execution vulnerability (CVE-2020-2506 & CVE-2020-2507). Threat actors are exploiting two unauthorized remote command execution vulnerabilities, tracked as CVE-2020-2506 & CVE-2020-2507, in the Helpdesk app that have been fixed by the vendor in October 2020.

CSO Magazine
APRIL 19, 2022
While significant progress is being made by global organizations in relation to threat detection and response, adversaries continue to surface, innovate, and adapt to target environments with diverse cyberattacks including new extortion and ransomware tactics, techniques, and procedures (TTPs).

Anton on Security
OCTOBER 20, 2022
Just as I did when I revisited my 2015 SOC nuclear triad blog in 2020 , I wanted to check if my opinions, views and positions from that time are still correct (spoiler: not exactly…) As a reminder, the post stated that most organizations building DIY security data lakes would not succeed in these glamorous endeavors.
Hacker's King
DECEMBER 16, 2024
The SolarWinds attack in 2020 is a prime example of cybercriminals infiltrating a software company and compromising its products, allowing them to access hundreds of organizations, including government agencies and Fortune 500 companies. Regular testing and updating of the plan ensures that organizations can respond quickly and effectively.

CyberSecurity Insiders
JANUARY 17, 2022
Knowing When to Move Threat Detection, Investigation and Response (TDIR) to the Cloud. What’s preventing organizations from allocating more funds to technologies that will make it easier to define, implement and operate effective threat detection, investigation and response (TDIR) programs? By Tyler Farrar, CISO, Exabeam.

CyberSecurity Insiders
FEBRUARY 15, 2021
So, on an average around 512 organizations were found to be hitting the networks of organizations out of which 14% of threats were already found to be incubating inside. Security researchers say that threats like phishing, scamming, extortion and business email compromise were found to be hitting the businesses on a serious note in 2020.

CyberSecurity Insiders
OCTOBER 24, 2021
SolarWinds, a software maker having 300,000 clients around the globe, was hit by a massive cyber attack in early 2020. And its staff detected it in November, after a security company named FireEye triggered a warning that the firm’s computer systems were operating under the control of hackers funded by a foreign nation from many days.

Anton on Security
FEBRUARY 10, 2023
Why Is Threat Detection Hard?” A SOC Tried To Detect Threats in the Cloud … You Won’t Believe What Happened Next” ”Top 10 SIEM Log Sources in Real Life?” Who Does What In Cloud Threat Detection?” “A What Does This Even Mean?!” “Who

Cisco Security
DECEMBER 6, 2021
Digital attacks grew in both volume and sophistication in 2020. As reported by PR Newswire , the number of complaints received by the FBI’s Cyber Division numbered as many as 4,000 a day during the first half of 2020—400% more than it was in the first few months of that year. The solution: extended threat detection and response (XDR).

Security Boulevard
AUGUST 9, 2024
In 2020, SQL injection-related CVEs were at 466. Similarly, XSS has seen an impressive climb, with CVEs jumping from 2,203 in 2020 to 5,179 in 2023, marking a substantial 135.08% rise. As we delve deeper, we encounter CSRF, which saw its CVEs grow from 416 in 2020 to an astounding 1,398 in 2023, marking an increase of 236.05%.

CyberSecurity Insiders
AUGUST 2, 2021
The well-experienced group of security professionals works on the security posture and obligations of their customer and draft a solution that meets all kinds of IT compliance obligations- as per the guidelines proposed in Security Legislation Amendment Bill 2020.

Anton on Security
MAY 25, 2022
Why Is Threat Detection Hard?” “A A SOC Tried To Detect Threats in the Cloud … You Won’t Believe What Happened Next” Top 5 Cloud Security Podcast by Google episodes: Episode 1“Confidentially Speaking” Episode 2 “Data Security in the Cloud” Episode 47 “Megatrends, Macro-changes, Microservices, Oh My!

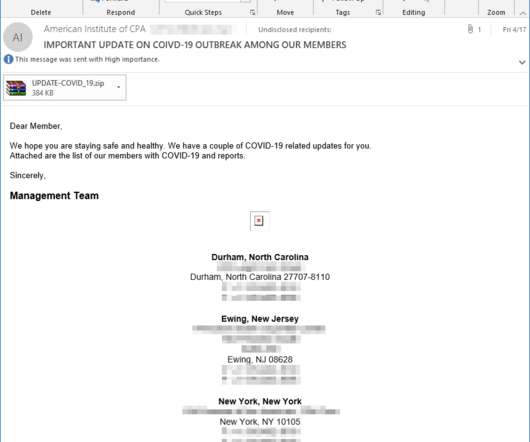
CyberSecurity Insiders
JUNE 21, 2021
Threat detection firm Avanan was the first to notify the users about the phishing campaign taking place worldwide and said that the phishing emails might also be loaded with links that when clicked could inject the device with malware. In the year 2019, Trend Micro detected over 61.2

Security Boulevard
JUNE 21, 2021
Can We Have “Detection as Code”?”. Why Is Threat Detection Hard?”. Security operations / detection & response: “Security Correlation Then and Now: A Sad Truth About SIEM”. “Can Can We Have “Detection as Code”?”. Revisiting the Visibility Triad for 2020”. Why is Threat Detection Hard?”. “A
Security Affairs
MAY 4, 2020
Microsoft warns of threat actors targeting organizations with malware-laced ISO and IMG files aimed at delivering a remote access trojan. Microsoft advanced machine learning threat detection models detected multiple malspam campaigns distributing malware-laced ISO.

Security Boulevard
MARCH 22, 2021
The cybersecurity landscape changed drastically on two fronts in 2020: volume and supply chain complexities. Attack surfaces expanded and softened as employees migrated off well-protected corporate networks and logged on from home.

Security Boulevard
MARCH 3, 2022
Can We Have “Detection as Code”?”. Why Is Threat Detection Hard?”. “A A SOC Tried To Detect Threats in the Cloud … You Won’t Believe What Happened Next”. Episode 27 “The Mysteries of Detection Engineering: Revealed!”. Episode 17 “Modern Threat Detection at Google”. Left of SIEM? Right of SIEM?

eSecurity Planet
JANUARY 28, 2021
billion in funding in 2020. In September 2020, Axis Security raised $32 million in Series B funding, for a total of $49 million over three rounds. Cado Security is a young startup, founded in 2020, yet it’s already received $1.5 In November 2020, Cato closed on a $130 million round of funding. Cato Networks.

Anton on Security
JUNE 21, 2021
Skills, Not Tiers” Top 5 posts with the most Medium fans : “Security Correlation Then and Now: A Sad Truth About SIEM” “Beware: Clown-grade SOCs Still Abound” “Can We Have “Detection as Code”?” “Why Why Is Threat Detection Hard?” “New New Paper: “Future of the SOC: SOC People?—?Skills, Skills, Not Tiers” Now, posts by topic.

eSecurity Planet
MAY 17, 2021
PowerShell was the source of more than a third of critical threats detected on endpoints in the second half of 2020, according to a Cisco research study released at the RSA Conference today.

The Last Watchdog
OCTOBER 16, 2023
The 2020 SolarWinds cybersecurity incident — which industry experts call the supply chain attack of the decade — was an incredibly high-profile breach affecting massive corporations. Data breaches exposed over 37 billion records in 2020 alone — a 141% jump from 2019. Simply put, cyberattacks are on the rise. Comprehensive Integration.
Security Affairs
MARCH 23, 2020
. “Starting from August 30, 2019, 360Netlab Threat Detection System has flagged multiple attack groups using LILIN DVR 0-day vulnerabilities to spread Chalubo [ 1] , FBot [ 2] , Moobot [ 3] botnets.” ” reads the advisory published by Netlab.
Anton on Security
NOVEMBER 6, 2023
The second part of the answer would be to outline the type of an organization that would very much prefer the decoupled SIEM where the best collection and modern storage somehow harmoniously work with the best threat detection and response content. (B)

Anton on Security
MARCH 29, 2021
Security operations / detection & response: “Security Correlation Then and Now: A Sad Truth About SIEM” “Beware: Clown-grade SOCs Still Abound” “Can We Have “Detection as Code”?” “New Skills, Not Tiers”” “Why is Threat Detection Hard?” New Paper: “Future of the SOC: SOC People?—?Skills,
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content