Evolution of threat landscape for IoT devices – H1 2018
Security Affairs
SEPTEMBER 19, 2018
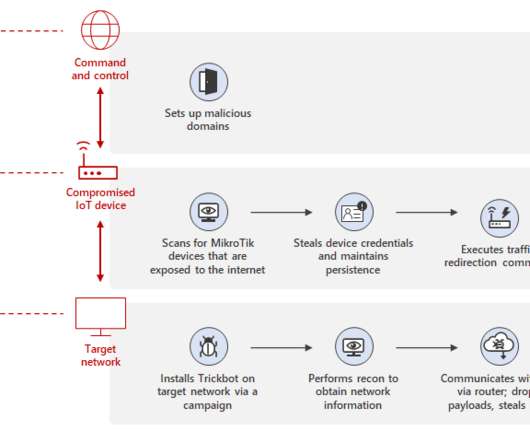
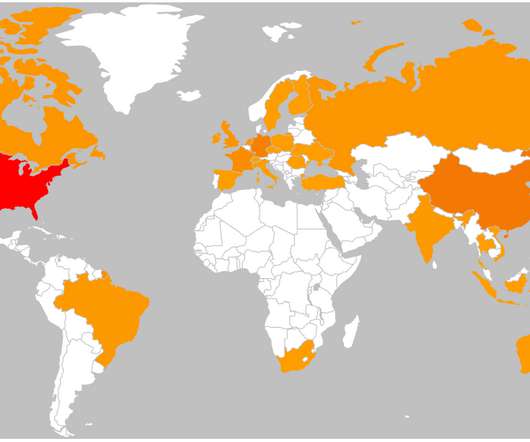
Security experts from Kaspersky have published an interesting report on the new trends in the IoT threat landscape. What is infecting IoT devices and how? The researchers set up a honeypot to collect data on infected IoT devices, the way threat actors infect IoT devices and what families of malware are involved.






























Let's personalize your content