$43 billion stolen through Business Email Compromise since 2016, reports FBI
The State of Security
MAY 5, 2022
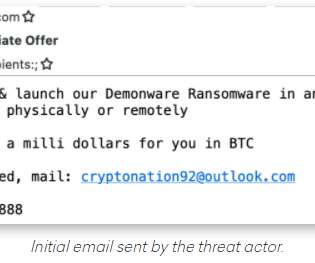
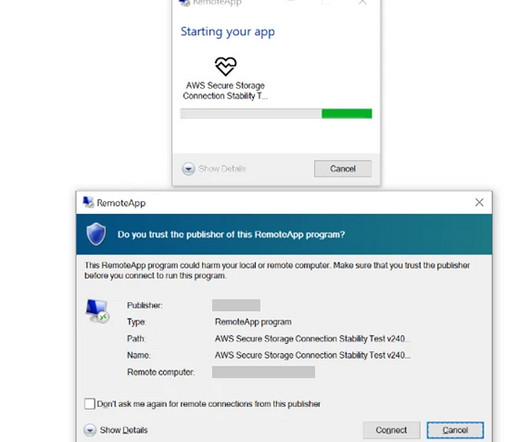
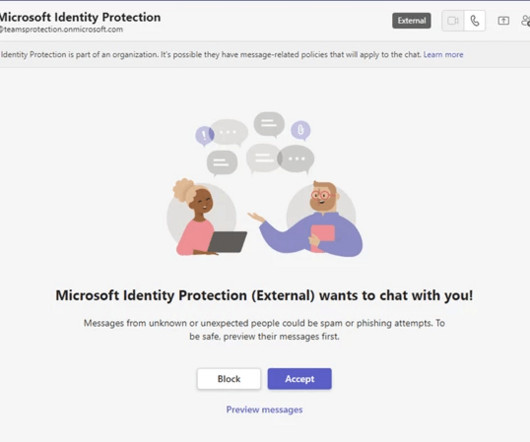
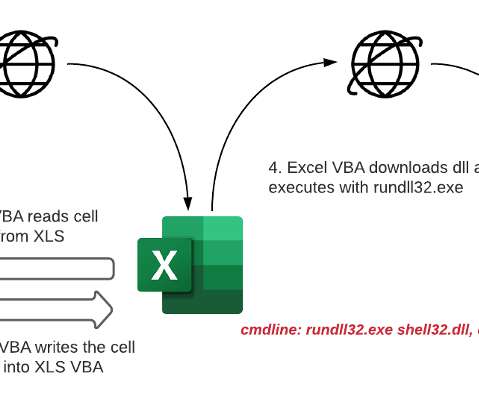
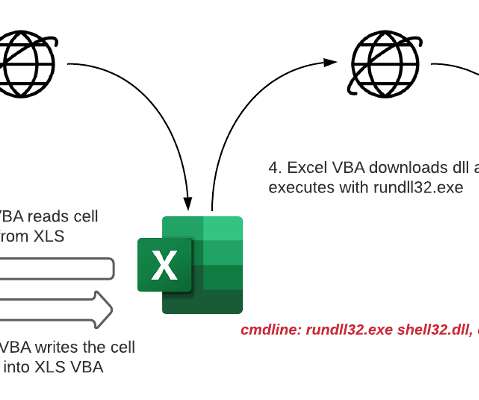
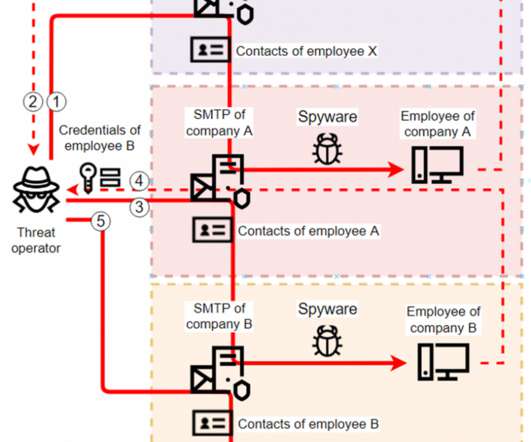
The FBI's Internet Crime Complaint Center (IC3) has issued updated statistics on Business Email Compromise (BEC) attacks which use a variety of social engineering and phishing techniques to break into accounts and trick companies into transferring large amounts of money into the hands of criminals.








































Let's personalize your content