CISA adds D-Link DIR router flaws to its Known Exploited Vulnerabilities catalog
Security Affairs
MAY 17, 2024
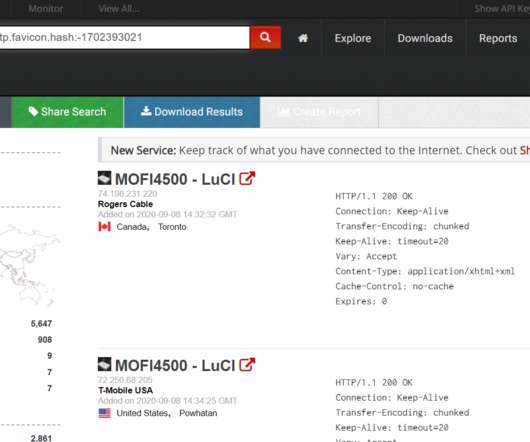
Cybersecurity and Infrastructure Security Agency (CISA) added the following D-Link router vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog : CVE-2014-100005 Multiple cross-site request forgery (CSRF) vulnerabilities in D-Link DIR-600 router (rev.



































Let's personalize your content