How Did Authorities Identify the Alleged Lockbit Boss?
Krebs on Security
MAY 13, 2024
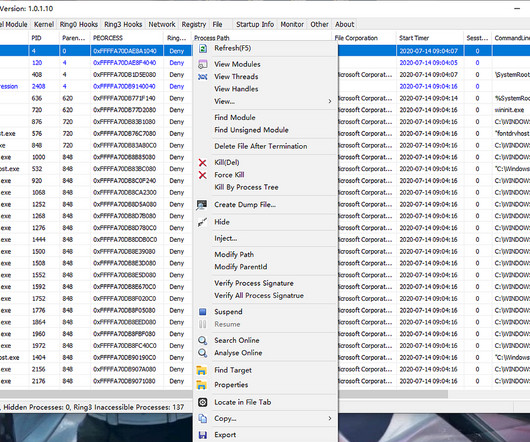
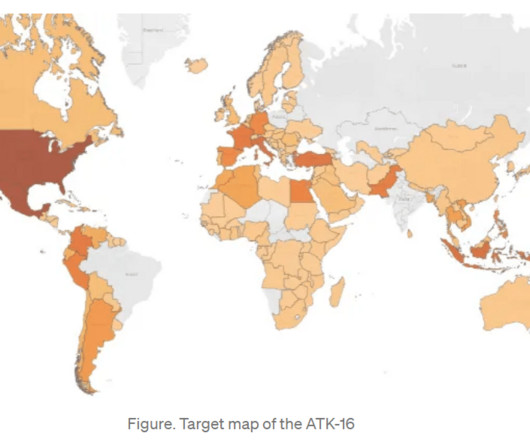
and Australia in sanctioning and charging a Russian man named Dmitry Yuryevich Khoroshev as the leader of the infamous LockBit ransomware group. 2011 said he was a system administrator and C++ coder. Last week, the United States joined the U.K. NeroWolfe’s introductory post to the forum Verified in Oct. “P.S.









Let's personalize your content