Who Is the Network Access Broker ‘Babam’?
Krebs on Security
DECEMBER 3, 2021
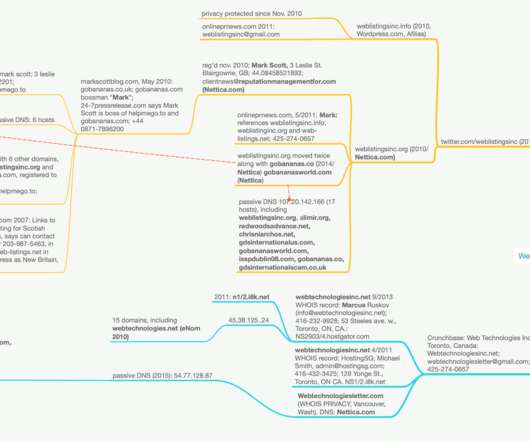
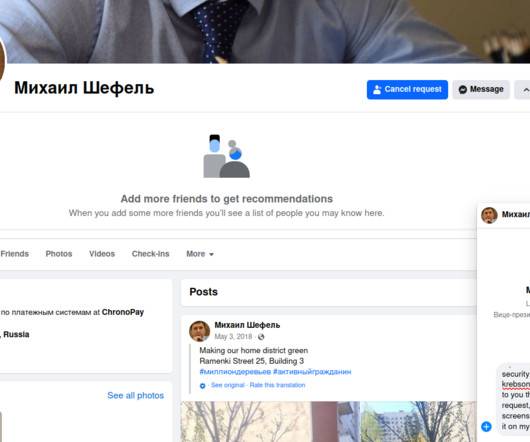
Cyber intelligence platform Constella Intelligence told KrebsOnSecurity that the operns@gmail.com address was used in 2016 to register an account at filmai.in , which is a movie streaming service catering to Lithuanian speakers. The username associated with that account was “ bo3dom.” com back in 2011, and sanjulianhotels[.]com










































Let's personalize your content