More Detail on the Juniper Hack and the NSA PRNG Backdoor
Schneier on Security
SEPTEMBER 9, 2021
Here’s me in 2007 on the NSA backdoor. We knew the basics of this story , but it’s good to have more detail. Here’s me in 2015 about this Juniper hack.

Schneier on Security
SEPTEMBER 9, 2021
Here’s me in 2007 on the NSA backdoor. We knew the basics of this story , but it’s good to have more detail. Here’s me in 2015 about this Juniper hack.
Cisco Security
OCTOBER 19, 2021
In any perimeter defense a key component is firewalls—the proverbial guard towers in your fortifications. In this Threat Trends release, we’ll be looking at Cisco Secure Firewall. The goal is to highlight the common threats that organizations encounter and block with Secure Firewall. Secure Firewall version 7.0
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Security Affairs
FEBRUARY 9, 2021
The NextGEN Gallery is one of the most popular WordPress gallery plugins that is available since 2007. We deploy firewall rules and reach out to Imagely. January 13, 2021 – Sites running the free version of Wordfence receive firewall rules. The plugin receives over 1.5

eSecurity Planet
MARCH 21, 2025
Check Point: Best for Firewalls 11 $25.34 Known for strong next-generation firewalls (NGFW) and endpoint detection and response (EDR) products, it also ranks for network security tools , zero trust , extended detection and response (XDR), IoT security , software-defined wide area network ( SD-WAN ), and secure access service edge (SASE).

eSecurity Planet
MAY 27, 2021
Next-generation firewalls NGFW Fortinet Palo Alto Networks. Web application firewall WAF Akamai Imperva. With comprehensive visibility across endpoints, automatic defensive mechanisms, and built-in firewalls, the Kaspersky EDR is a global leader in making endpoint protection seamless. Next-Generation Firewalls (NGFW): Fortinet.
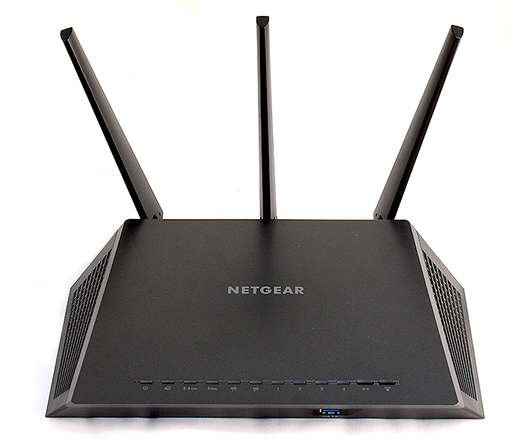
Security Affairs
JUNE 18, 2020
Oldest firmware versions have been released as far back as 2007. “This could be accomplished in a number of ways, most notably with firewall rules/whitelisting.” A whopping 79 Netgear router models are vulnerable to a severe security flaw that can let hackers take over devices remotely.

eSecurity Planet
AUGUST 13, 2021
Gartner gave it top place in unified threat management (UTM), and it was named a Leader in next-gen firewalls (NGFW). Over the years, it has built up a wide range of security products, including firewalls, intrusion prevention systems (IPS), UTM, malware protection and cloud protection. Learn more about Fortinet. Visit website.
Let's personalize your content