Access Governance Strategy and Technology: How to Plan It Well
Heimadal Security
JULY 12, 2023
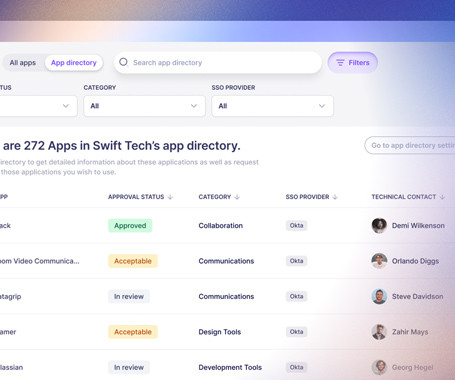
Over the past couple of years, increasingly more sysadmins have abandoned the more “traditional”, hands-on, approach to access and identity management in favor of IAG (Identity and Access Governance).









































Let's personalize your content