Palo Alto Firewalls Under Attack: Critical Flaw Exploited to Deploy Cryptojacking Malware
Penetration Testing
APRIL 28, 2024
Palo Alto Networks’ popular firewall appliances are currently in the crosshairs of cybercriminals.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Penetration Testing
APRIL 28, 2024
Palo Alto Networks’ popular firewall appliances are currently in the crosshairs of cybercriminals.
eSecurity Planet
JUNE 28, 2023
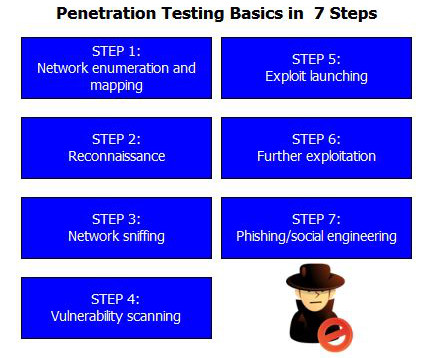
Penetration tests are vital components of vulnerability management programs. In these tests, white hat hackers try to find and exploit vulnerabilities in your systems to help you stay one step ahead of cyberattackers. Here we’ll discuss penetration testing types, methods, and determining which tests to run.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

eSecurity Planet
FEBRUARY 25, 2022
Many cybersecurity audits now ask whether penetration testing is conducted and how vulnerabilities are detected and tracked. These questions ask IT teams to consider how frequently security is tested from the outside via penetration testing and from the inside via vulnerability testing. File servers.

eSecurity Planet
JUNE 23, 2023
All organizations should perform penetration tests, yet many worry about not receiving the full value of their investment. Organizations have two choices: perform penetration tests with their internal teams, or hire an external vendor and find ways to lower costs.

Penetration Testing
APRIL 12, 2024
Palo Alto Networks has disclosed a severe zero-day vulnerability (CVE-2024-3400) affecting its market-leading firewall software, PAN-OS. This vulnerability carries a CVSS score of 10.0, indicating its critical severity.

Penetration Testing
JANUARY 28, 2024
Features Full IP/TCP... The post OpenGFW: flexible, open-source implementation of Great Firewall on Linux appeared first on Penetration Testing. It’s cyber sovereignty you can have on a home router.

Penetration Testing
FEBRUARY 4, 2024
Recently, two security vulnerabilities have been identified in Malwarebytes Binisoft Windows Firewall Control, a widely-used tool that enhances the capabilities of the Windows Firewall.

Penetration Testing
DECEMBER 31, 2023
PingRAT PingRAT secretly passes C2 traffic through firewalls using ICMP payloads.

Penetration Testing
MARCH 28, 2024
A newly discovered vulnerability in Imperva SecureSphere, a widely used on-premise Web Application Firewall (WAF), has the potential to expose organizations to devastating security breaches.

Penetration Testing
FEBRUARY 20, 2024
Zyxel’s recent security advisory spotlights multiple vulnerabilities present in select firewall and access point models. Vulnerability Breakdown CVE-2023-6397 (Firewalls): Potential denial-of-service... The post Zyxel Security Vulnerabilities: DoS, Command Injection & More appeared first on Penetration Testing.

eSecurity Planet
FEBRUARY 21, 2024
A firewall audit is a procedure for reviewing and reconfiguring firewalls as needed so they still suit your organization’s security goals. Auditing your firewall is one of the most important steps to ensuring it’s still equipped to protect the perimeter of your business’ network.

eSecurity Planet
JANUARY 5, 2024
A firewall policy is a set of rules and standards designed to control network traffic between an organization’s internal network and the internet. Featured Partners: Next-Gen Firewall (NGFW) Software Learn more Table of Contents Toggle Free Firewall Policy Template What Are the Components of Firewall Policies?
Penetration Testing
APRIL 24, 2024
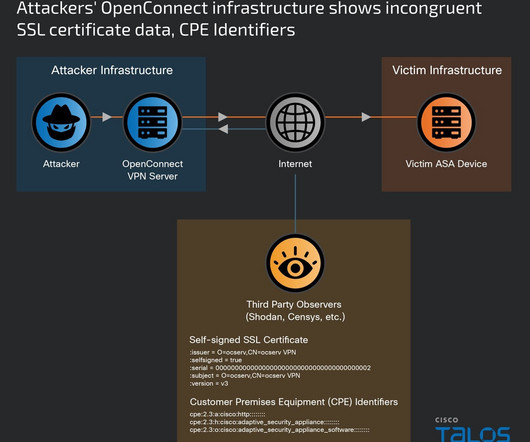
A sophisticated and ongoing cyberattack dubbed “ArcaneDoor” has breached Cisco firewalls across the globe.

Penetration Testing
MARCH 12, 2024
Security researcher ‘stealthcopter‘ has exposed a severe security hole in the widely used WordPress Anti-Malware Security and Brute-Force Firewall plugin (GOTMLS). could allow... The post CVE-2024-22144: Critical Flaw in Popular WordPress Security Plugin Exposes 200,000+ Sites appeared first on Penetration Testing.

eSecurity Planet
APRIL 30, 2024
Setting up a firewall is the first step in securing your network. A successful firewall setup and deployment requires careful design, implementation, and maintenance to effectively improve your network integrity and data security. Verify that the chosen firewall can meet your security standards and functions.

Penetration Testing
JANUARY 31, 2024
Developed by Trustwave’s SpiderLabs, this open-source web application firewall (WAF) engine supports Apache, IIS, and Nginx. It’s... The post CVE-2024-1019: Exposing ModSecurity’s Critical WAF Bypass Flaw appeared first on Penetration Testing.

Penetration Testing
FEBRUARY 10, 2024
A new menace emerged, dubbed “KV-botnet,” this sophisticated malware network was identified by Lumen’s Black Lotus Labs, revealing a covert operation that had infected small-office and home-office routers and firewall devices globally.

Penetration Testing
APRIL 11, 2022
Open Source API Firewall API Firewall is a high-performance proxy with API request and response validation based on OpenAPI/Swagger schema. It provides API... The post API Firewall v0.6.14 releases: Fast and light-weight API proxy firewall appeared first on Penetration Testing.

eSecurity Planet
OCTOBER 31, 2023
A penetration testing report discloses the vulnerabilities discovered during a penetration test to the client. Penetration test reports deliver the only tangible evidence of the pentest process and must deliver value for a broad range of readers and purposes.

Penetration Testing
APRIL 3, 2021
Go Test WAF GoTestWAF is a tool for API and OWASP attack simulation, that supports a wide range of API protocols including REST, GraphQL, gRPC, WebSockets, SOAP, XMLRPC, and others. releases: test different web application firewalls (WAF) for detection logic and bypasses appeared first on Penetration Testing.
Security Boulevard
APRIL 26, 2022
The post 5 secure ways to configure a Firewall appeared first on Kratikal Blogs. The post 5 secure ways to configure a Firewall appeared first on Security Boulevard. Visiting another website requires connection to a specialized computer called a web server, which, like any […].

Penetration Testing
MARCH 29, 2018
The pfSense project is a free network firewall distribution, based on the FreeBSD operating system with a custom kernel and including third-party free software packages for additional functionality. released: free network firewall distribution appeared first on Penetration Testing.

SiteLock
OCTOBER 21, 2021
Let us start with the abbreviations that define the categories of information security products: WAF stands for Web Application Firewall , NGFW stands for Next Generation Firewall. NGFW (or Next Generation Firewall) is an evolution of traditional firewalls and serves to delimit access between network segments.

CyberSecurity Insiders
MAY 28, 2023
Research network security mechanisms, such as firewalls, intrusion detection systems (IDS), and virtual private networks (VPNs). Learn about secure coding practices, web application firewalls (WAFs), and vulnerability scanning tools. Explore IoT security architectures, protocols, and solutions for securing interconnected devices.

Penetration Testing
AUGUST 1, 2019
frp is a fast reverse proxy to help you expose a local server behind a NAT or firewall to the internet. releases: fast reverse proxy for exposing a local server behind a NAT or firewall to the internet appeared first on Penetration Testing.

The Last Watchdog
MARCH 15, 2021
Related: Integrating ‘pen tests’ into firewalls. Penetration tests are one way of mitigating the security risks that arise and make sure that we are not endangering users, their data, and the trust they inherently place in technology. Depending on the scope of the test, many different results can be achieved.

NopSec
NOVEMBER 6, 2014
11.3 – Implement a Methodology for Penetration Testing This requirement states the establishment of a penetration testing methodology. 11.3 – Implement a Methodology for Penetration Testing This requirement states the establishment of a penetration testing methodology. starting June 30, 2015.

Schneier on Security
AUGUST 29, 2018
When the compromise was suspected, the FBI and NSA both ran "penetration tests" to determine the security of the interim system. In the words of one of the former officials, the CIA had "f *d up the firewall" between the two systems.

eSecurity Planet
JUNE 20, 2023
After surveying trusted penetration testing sources and published pricing, the cost of a penetration test for the average organization is $18,300. and different types of penetration tests (black box, gray box, white box, social engineering, etc.).

Zigrin Security
AUGUST 9, 2023
Penetration testing is how you find out, but with three main types, black-box, grey-box, and white-box, how do you choose? Penetration tests can sound intimidating, but it’s one of the best ways to identify vulnerabilities before the bad guys do. black-box penetration testing is for you! Thrill seekers!

Security Affairs
MARCH 24, 2023
it was first discovered by Michael Mazzolini from penetration testing firm GoldNetwork. “We developed a Proof of Concept and began writing and testing a firewall rule immediately. The vulnerability impacts plugin versions 4.8.0 through 5.6.1, ” reads the advisory published by Wordfence.

Penetration Testing
JANUARY 8, 2020
wstunnel Most of the time when you are using a public network, you are behind some kind of firewall or proxy. releases: Tunneling over websocket protocol appeared first on Penetration Testing. One of their purposes is to constrain you to only use certain kinds... The post wstunnel v8.0

Penetration Testing
OCTOBER 5, 2019
netassert netassert: network security testing for DevSecOps workflows This is a security testing framework for fast, safe iteration on the firewall, routing, and NACL rules for Kubernetes (Network Policies, services) and non-containerised hosts (cloud... The post netassert v2.0.3

The Last Watchdog
FEBRUARY 28, 2022
WAF (Web Application Firewall) employs setting rules based on IP addresses, and monitoring traffics to block malicious IPs. DAST (Dynamic Application Security Testing) lacks the context of APIs with automated testing and requires costly first time manual Penetration testing effort. Tool limitations.

Security Affairs
NOVEMBER 25, 2020
“Retailers must take meaningful steps to protect consumers’ credit and debit card information from theft when they shop,” said Massachusetts AG Maura Healey. ” .

eSecurity Planet
MARCH 4, 2021
Use web application and database firewalls. Your database server should be protected from database security threats by a firewall, which denies access to traffic by default. The firewall should also protect your database from initiating outbound connections unless there is a specific need to do so. Secure database user access.

eSecurity Planet
APRIL 29, 2024
Siemens issued a notice that the RUGGEDCOM APE 1808, an industrial platform hardened for harsh physical environments, could come pre-installed with Palo Alto next generation firewalls vulnerable to the Pan-OS vulnerability. There is no workaround available, and the published proof of concept will probably allow attacks in the near future.
eSecurity Planet
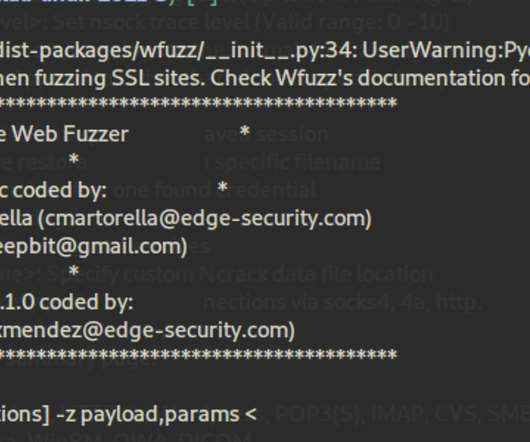
FEBRUARY 24, 2022
Here we’re focusing on some lesser-known but still worthy open-source solutions that can be used separately for specific purposes or combined to run comprehensive penetration tests. Can bypass a victim’s firewall. The post 10 Top Open Source Penetration Testing Tools appeared first on eSecurityPlanet.

eSecurity Planet
DECEMBER 10, 2023
Firewalls monitor and control incoming and outgoing traffic while also preventing unauthorized access. Overlapping rules may impair firewall efficiency or expose flaws that allow attackers to circumvent regulations. Choose a centralized platform that is interoperable with several firewall suppliers.

The Last Watchdog
AUGUST 20, 2018
Related: Why identities are the new firewall. Vulnerability scanning and penetration testing can help to identify weaknesses and areas where networks have not been configured correctly. based cybersecurity professional; his 15 years IT experience, includes penetration testing and ethical hacking projects.

Security Affairs
JANUARY 28, 2023
In fact, in this case, the attackers were able to exploit unpatched vulnerabilities in the company’s FortiGate firewall. Threat Actor Brief LockBit is a well-known ransomware affiliation program started back in September 2019, where the developers use third parties to spread the ransomware by hiring unethical penetration testing teams.
Security Affairs
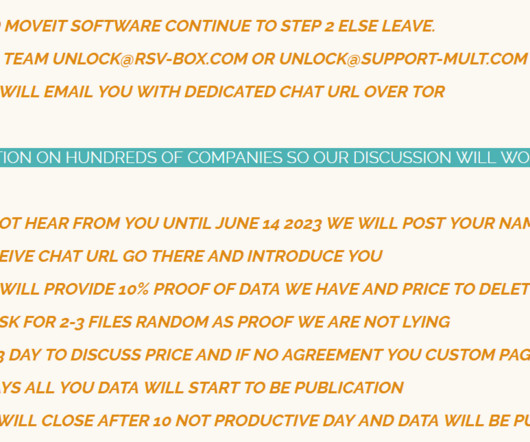
JUNE 16, 2023
Customers have to modify firewall rules to deny HTTP and HTTPs traffic to the software on ports 80 and 443. WE ALSO WANT TO REMIND ALL COMPANY THAT IF YOU PUT DATA ON INTERNET WHERE DATA IS NOT PROTECT DO NOT BLAME US FOR PENETRATION TESTING SERVICE. Disable all HTTP and HTTPs traffic to your MOVEit Transfer environment.

Zigrin Security
OCTOBER 11, 2023
For a detailed threat actor description do not forget to check out our blog article about selecting between black-box, white-box, and grey-box penetration tests and also you would know which pentest you need against a specific threat actor. Regularly conduct cybersecurity training sessions to reinforce good security habits.

SiteLock
AUGUST 27, 2021
Unlike firewalls, CDNs by themselves cannot block bad bots from infecting a website. You need to learn how often the data is cached and how often penetration testing is completed to ensure the server is secure. Use a Web Application Firewall. CDN Security Concerns. Are there failover security measures in place?
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content