How blockchain could revolutionize IoT security
Tech Republic Security
JULY 17, 2017
There may be a way to secure processing-starved IoT devices by using a new approach to blockchain. Read about researchers' proposal.

Tech Republic Security
JULY 17, 2017
There may be a way to secure processing-starved IoT devices by using a new approach to blockchain. Read about researchers' proposal.
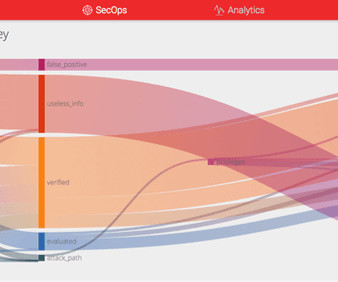
NopSec
JULY 19, 2017
Here at NopSec, we have always been fascinated with automation. It has been a focus of ours since the beginning of our cybersecurity SaaS solution launch, Unified VRM , back in 2012. We first tackled the complexity of correlating several commercial and open-source networks and web application scanner’s results by automating the import of results via files or directly via API.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Tech Republic Security
JULY 17, 2017
Amid a shortage of skilled cybersecurity professionals, here are the three positions in the field that companies are seeking out the most, according to tech staffing firm Mondo.

Tech Republic Security
JULY 21, 2017
It's only a matter of time before another WannaCry-style ransomware outbreak, but you don't have to be a victim. Here's what IT leaders need to know in order to safeguard themselves and their users.

Advertisement
How many people would you trust with your house keys? Chances are, you have a handful of trusted friends and family members who have an emergency copy, but you definitely wouldn’t hand those out too freely. You have stuff that’s worth protecting—and the more people that have access to your belongings, the higher the odds that something will go missing.

Tech Republic Security
JULY 20, 2017
Hardware can fail and malware happens to the best of us. Don't be caught without the ability to restore a computer: Use one of these 10 free backup programs instead.

Tech Republic Security
JULY 19, 2017
Leon Kuperman, CTO of CUJO IoT Security, why your small business and home office needs a firewall, and why your ISP can't protect you from bad IPs, phishing links, and sites loaded with malware.
Cyber Security Informer brings together the best content for cyber security professionals from the widest variety of industry thought leaders.

Tech Republic Security
JULY 19, 2017
A new report from Enigma Software Group compared the malware infection rates in all 50 states over the first six months of 2017. Here are the results.

Tech Republic Security
JULY 20, 2017
A recent blog from Senrio detailed a new flaw called Devil's Ivy, found in an open source code library, that could be used to hijack security cameras and for other nefarious purposes.

Tech Republic Security
JULY 19, 2017
Hacking incidents cost companies millions of dollars on average. Here's why the CFO needs to be involved in cybersecurity strategies from the start.

Tech Republic Security
JULY 17, 2017
IBM recently unveiled its latest mainframe, IBM Z, with an encryption engine capable of protecting company data in the cloud, in an application, and in a database.

Advertiser: Revenera
In a recent study, IDC found that 64% of organizations said they were already using open source in software development with a further 25% planning to in the next year. Most organizations are unaware of just how much open-source code is used and underestimate their dependency on it. As enterprises grow the use of open-source software, they face a new challenge: understanding the scope of open-source software that's being used throughout the organization and the corresponding exposure.

Tech Republic Security
JULY 20, 2017
If you constantly log in and out of your servers with ssh, Jack Wallen shows you how to make this task a bit more efficient, with the help of ssh-agent.

Tech Republic Security
JULY 20, 2017
IBM has partnered with Borsa Italiana, part of London Stock Exchange Group, in an effort to digitize securities certificate data for smaller companies.

Tech Republic Security
JULY 20, 2017
Determining the source of locked accounts can be difficult and time-consuming. Use this technique to help troubleshoot this problem.

Tech Republic Security
JULY 18, 2017
Inviting people to find flaws in your system might sound crazy. But who would you rather discover a bug: someone working for you, or against you?

Advertisement
The healthcare industry has massively adopted web tracking tools, including pixels and trackers. Tracking tools on user-authenticated and unauthenticated web pages can access personal health information (PHI) such as IP addresses, medical record numbers, home and email addresses, appointment dates, or other info provided by users on pages and thus can violate HIPAA Rules that govern the Use of Online Tracking Technologies by HIPAA Covered Entities and Business Associates.

Tech Republic Security
JULY 19, 2017
A new startup aims to commercialize a security approach birthed at Google. It just might work.

Tech Republic Security
JULY 20, 2017
As attack vectors evolve, so too do hacker tactics. Mike Cotton, VP of Research and Development at Digital Defense, explains how automation helps companies prepare for the next attack.

Tech Republic Security
JULY 21, 2017
Nexusguard's CTO Juniman Kasman explains how the hybrid cloud helps cybersecurity firms differentiate between legitimate traffic and fake IP addresses used for denial of service attacks.

Tech Republic Security
JULY 17, 2017
Encryption safeguards your company's most sensitive data. Access Now's U.S. Policy Manager Amie Stepanovich explains why a proposal by the Australian Prime Minister threatens the safety of data around the world.

Speaker: Blackberry, OSS Consultants, & Revenera
Software is complex, which makes threats to the software supply chain more real every day. 64% of organizations have been impacted by a software supply chain attack and 60% of data breaches are due to unpatched software vulnerabilities. In the U.S. alone, cyber losses totaled $10.3 billion in 2022. All of these stats beg the question, “Do you know what’s in your software?

Tech Republic Security
JULY 18, 2017
Travis Farral, Director of Security Strategy at Anomali, explains why ransomware attacks occur, how they spread, and what organizations can do to keep data secure.

Tech Republic Security
JULY 18, 2017
Why invite people to look into your code and try to find flaws? Here are five good reasons.

NopSec
JULY 18, 2017
CIS 20 Security Controls represent one of the reference frameworks of the most critical controls an organization can implement to establish a well balanced security program to safeguard confidentiality, integrity and availability of information. It provides a detailed guide for prioritization, implementation and customization of your security controls as well as sequence, test, and achieve continuous automation.
Let's personalize your content